MobiHok v6 Cracked
The word “Mobihok” has become famous in the cybersecurity community. Mobile Hacking, or Mobihok for short, is a notoriously dangerous Remote Access Trojan (RAT). From its humble beginnings as Mobihok v6, it has developed into a powerful instrument for criminal and cyber espionage purposes. This essay will explore the different forms of Mobihok, how it came to be, and the threats it presents to both individuals and businesses.
Attackers gain full control over infected devices when they use Mobihok, a RAT. Without the victim’s knowledge, it can secretly record, monitor, and modify their gadget. The ability to steal login passwords, personal data, and financial information is made possible by this, making it a valuable tool for cybercriminals.
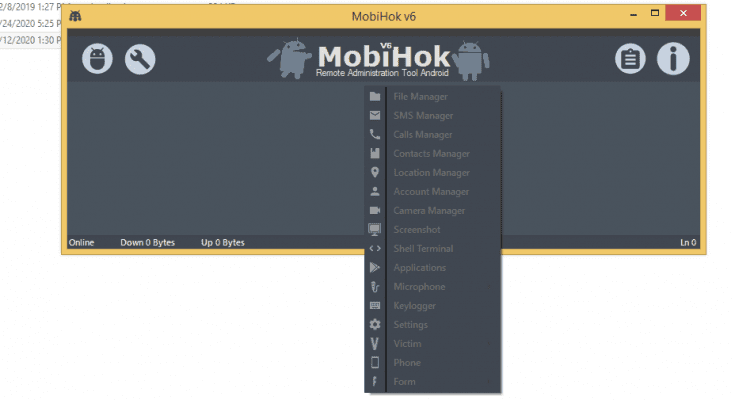
There have been multiple iterations of Mobihok, and each one has improved over the last. Features including keylogging, screen recording, and remote control of infected devices were introduced in Mobihok v6. Victims’ keystrokes, screenshots, and even remote device control can be monitored by attackers using these functionalities.
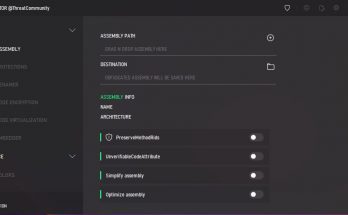
The potential of Mobihok to avoid detection by conventional antivirus software is a very worrying component of the malware. Antivirus software has a hard time detecting and removing Mobihok because the malware’s developers are always adding new features that circumvent security protections. This means that malware like Mobihok can infect even antivirus-protected devices.
Mobihok poses a great deal of risk. It can lead to financial loss, invasion of privacy, and identity theft for individuals. Data breaches, IP theft, and reputational harm are all possible outcomes for organizations. Criminals and state-sponsored hackers using Mobihok is a major risk to our country’s security.
Supported all versions of android
Generates FUD payload
Victim live screen recording streaming
Bind payload with another apk
Persistence payload
Social Media phishing pages
Stable connection
Easy to use
File manager
SMS manager
Calls manager
Contacts manager
Location manager
Account manager
Camera manager
Live screenshot of victims
Shell terminal
Application
Directly install any another apk on victims phone
Microphone
Keylogger
Settings
Victim
Phone
Many More…
Download
Choose a convenient way for you to download and download the file.
If the archive asks for a password, enter – enesoftware
| Mirrored | Download |
| Mega | Download |
| Ya.Disk | Download |
| Torrent File | |
| Download by magnet-link | |
| Loclouds | Download |
| Alternative link for bypassing blockades | Download |
To download files via Torrent File or magnet-link you need to download a torrent client. I recommend using utorrent
You can download the installer from our partners.