jSpy v0.31 Cracked
jSpy v0.31 Cracked
Many trojans and backdoors now have remote administration capabilities allowing an individual to control the victim’s computer.
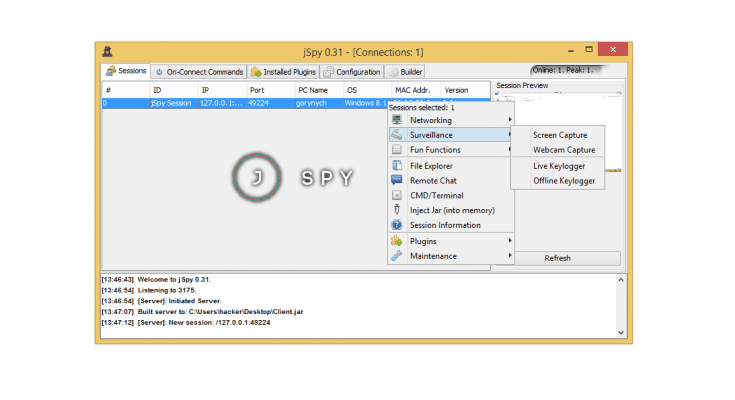
jSpy lurks in the shadows of the digital world, classified as a Remote Administration Tool (RAT). This malicious software grants unauthorized access to a victim’s computer, transforming it into a puppet controlled by the attacker. Understanding jSpy’s capabilities is crucial to safeguard oneself from its intrusive grasp.
jSpy’s functionality revolves around espionage and control. It allows attackers to peer into the infected device, potentially stealing sensitive data like passwords, financial information, and personal files. Furthermore, jSpy empowers them to manipulate the system, enabling actions such as installing additional malware, disrupting operations, or even deploying ransomware attacks.
The pervasiveness of jSpy is a cause for concern. While technical details remain under wraps to avoid aiding malicious actors, security researchers have identified various versions, highlighting its ongoing development.
Combating jSpy necessitates a multi-pronged approach. Utilizing robust antivirus and anti-malware software with up-to-date definitions is paramount for identifying and neutralizing the threat. Practicing safe browsing habits and avoiding suspicious downloads are additional layers of defense.
In conclusion, jSpy malware poses a significant threat to digital privacy and security. By recognizing its capabilities and implementing preventative measures, individuals can take back control and protect themselves from this insidious software.
Many times, a file (often called a client or stub) must be opened on the victim’s computer before the hacker can have access to it. These are generally sent through email, P2P file sharing software, and in internet downloads. They are usually disguised as a legitimate program or file. Many clients/stubs will display a fake error message when opened, to make it seem like it didn’t open. Some will also disable antivirus and firewall software. RAT trojans can generally do the following:
Block mouses and keyboards
Change the desktop wallpapers
Downloads, uploads, deletes, and rename files
Destroys hardware by overclocking
Drop viruses and worms
Edit Registry
Use your internet connection to perform denial of service attacks (DoS)
Format drives
Steal passwords, credit card numbers
Alter your web browser’s homepage
Hide desktop icons, task bar and files
Silently install applications
Log keystrokes, keystroke capture software
Open CD-ROM tray
Overload the RAM/ROM drive
Send message boxes
Play sounds
Control mouse or keyboard
Record sound with a connected microphone
Record video with a connected webcam
Show fake errors
Shutdown, restart, log-off, shut down monitor
Record and control victim’s screen remotely
View, kill, and start tasks in task manager
Let the hacker surf the web with the IP-address of the infected computer
A well-designed RAT will allow the operator the ability to do anything that they could do with physical access to the machine. Some RAT trojans are pranks that are most likely being controlled by a friend or enemy on April Fool’s Day or a holiday. Prank RATs are generally not harmful, and won’t log keystrokes or store information about the system on the computer. They usually do disruptive things like flip the screen upside-down, open the CD-ROM tray, or swap mouse buttons.
Download
Choose a convenient way for you to download and download the file.
If the archive asks for a password, enter – enesoftware
| Mirrored | Download |
| Mega | Download |
| Ya.Disk | Download |
| Torrent File | |
| Download by magnet-link | |
| Loclouds | Download |
| Alternative link for bypassing blockades | Download |
To download files via Torrent File or magnet-link you need to download a torrent client. I recommend using utorrent
You can download the installer from our partners.